From the warm-and-fuzzy recordsdata comes this feel-good Friday submit, chronicling this week’s takedown of 2 hated ransomware teams. One vanished on Tuesday, allegedly after being hacked through a gaggle claiming allegiance to Ukraine. The opposite used to be taken out an afternoon later due to a world police dragnet.
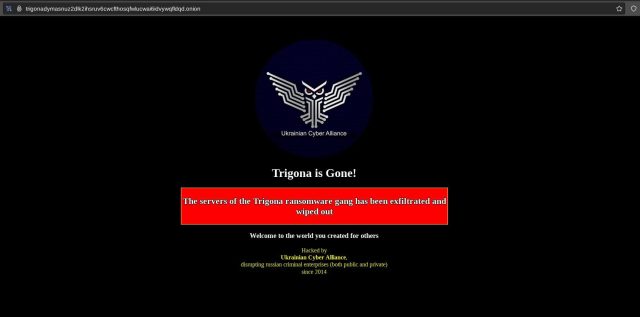
The primary team, calling itself Trigona, noticed the content material on its darkish internet sufferer naming-and-shaming website online pulled down and changed with a banner proclaiming: “Trigona is long past! The servers of Trigona ransomware gang has been infiltrated and burnt up.” An outfit calling itself Ukrainian Cyber Alliance took credit score and integrated the tagline: “disrupting Russian prison enterprises (each private and non-private) since 2014.”
Deficient operational safety
A social media post from a consumer claiming to be a Ukrainian Cyber Alliance press secretary stated his team centered ransomware teams partially as a result of they imagine themselves out of achieve of Western legislation enforcement.
“We simply discovered one gang like that and did to them as they do to the remaining,” the clicking secretary wrote. “Downloaded their servers (ten of them), deleted the whole thing and defaced for the closing time. TOR did not lend a hand them and even understanding that they had a hollow in it. Their complete infrastructure is totally blown away. The sort of hunt ahead.’”
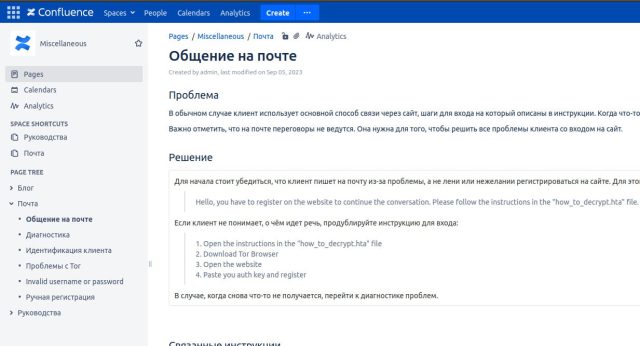
A separate social media post dumped what the clicking secretary stated used to be an administrative panel key and stated the crowd burnt up Trigona’s “touchdown, weblog, leaks website online, inside server (rocketchat, atlassian), wallets and dev servers.” The individual additionally claimed that the Ukrainian Cyber Alliance hacked a Confluence server Trigona used.
By means of Friday, the Trigona website online used to be unavailable, as evidenced through the message “Onionsite now not discovered.”
Trigona first surfaced in 2022 with shut ties to ransomware teams referred to as CryLock and BlackCat and looser ties to ALPHV. It basically hacked corporations in the USA and India, adopted through Israel, Turkey, Brazil, and Italy. It used to be recognized for compromising MYSQL servers, regularly through brute forcing passwords. A June profile of the crowd through researchers from safety company Development Micro famous that the crowd’s technical sophistication used to be combined.
“The Trigona ransomware team has deficient operational safety in the case of the implementation of Tor websites—even though their intention of focused on poorly controlled SQL servers isn’t one thing we typically see with much less technically talented danger actors,” the submit mentioned.
The timeline of the hack, in keeping with the social media posts, means that the breach started kind of 8 days in the past, with the hack of a Confluence server Trigona participants used to collaborate. In an interview with the Document, the crowd stated it deliberate to show over knowledge it seized to legislation enforcement government.
A takedown 2 years within the making
The second one ransomware gang takedown this week came about to Ragnar Locker, a gaggle that has hacked a lot of organizations international. On Friday, Europol said:
In an motion performed between 16 and 20 October, searches had been carried out in Czechia, Spain and Latvia. The “key goal” of this malicious ransomware pressure used to be arrested in Paris, France, on 16 October, and his house in Czechia used to be searched. 5 suspects had been interviewed in Spain and Latvia within the following days. On the finish of the motion week, the principle wrongdoer, suspected of being a developer of the Ragnar team, has been introduced in entrance of the inspecting magistrates of the Paris Judicial Court docket.
The ransomware’s infrastructure used to be additionally seized within the Netherlands, Germany and Sweden and the related knowledge leak web page on Tor used to be taken down in Sweden.
Ragnar Locker emerged in 2019 and briefly changed into recognized for its luck in hacking organizations in quite a lot of sectors, together with well being care, executive, generation, finance, training, and media. It’s what’s referred to as a RAAS (ransomware as a carrier), during which core participants broaden the encryption tool, run a central server, after which paintings with associates. The associates then hack sufferers, and income are divided between the 2 teams. Extra in regards to the team is to be had here and here.
Friday’s Europol submit stated Ragnar Locker participants warned sufferers to not touch government as a result of they might most effective “muck issues up.”
In truth, Europol participants, at the side of the FBI and Ukrainian government, have been investigating the crowd since 2021 and frequently made development, culminating on this week’s arrest and takedown.
“Little did they know that legislation enforcement used to be last in on them,” Europol stated.


